Igleak Info App 2026 Vault HQ Vids/Pics Direct
Claim Your Access igleak info app select streaming. No subscription costs on our on-demand platform. Immerse yourself in a endless array of selections presented in superb video, suited for exclusive watching devotees. With fresh content, you’ll always keep current. Watch igleak info app tailored streaming in amazing clarity for a genuinely engaging time. Join our community today to look at exclusive prime videos with zero payment required, access without subscription. Look forward to constant updates and discover a universe of distinctive producer content optimized for deluxe media lovers. You won't want to miss specialist clips—get a quick download! Discover the top selections of igleak info app visionary original content with breathtaking visuals and featured choices.
Check igleak.info with our free review tool and find out if igleak.info is legit and reliable Telephone number, date of birth or address), has been made. Instagram generatormobile device requiredinstagram generator
IG Leak 046 · Scaling With Social Media
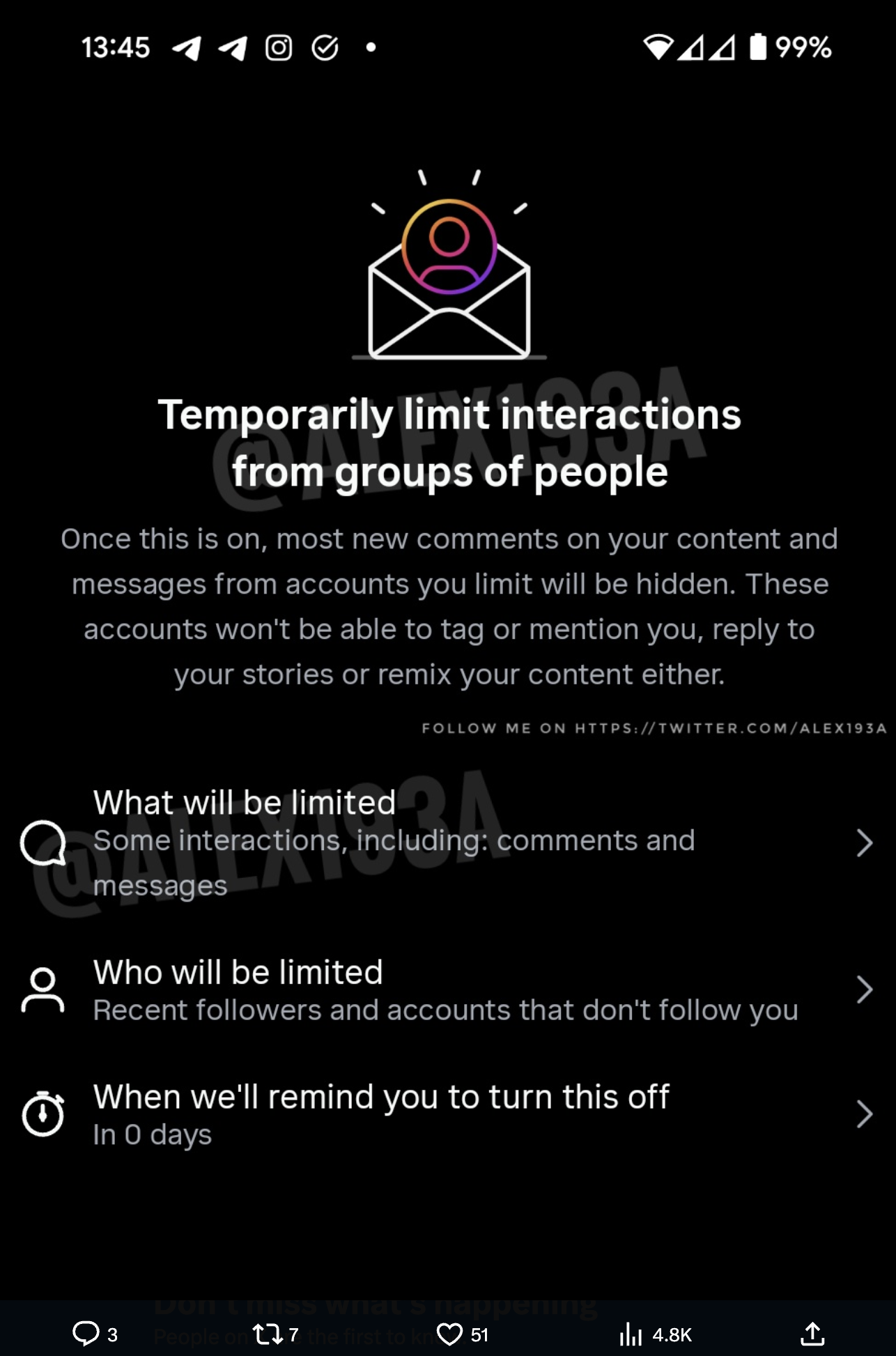
Important distinction when discussing this as saying hacks can give the idea that someone is accessing your dm's through apps or code, when the reality of this is that it's a common scam tricking you to give away your password or login info. With the hpi identity leak checker, it is possible to check whether your email address, along with other personal data (e.g The personal details of up to six million instagram users have reportedly been leaked online after a bug in the platform made profiles' account information publicly accessible.
Trustedsite offers an earned certification program for online businesses to help shoppers identify secure sites that demonstrate good business practices.
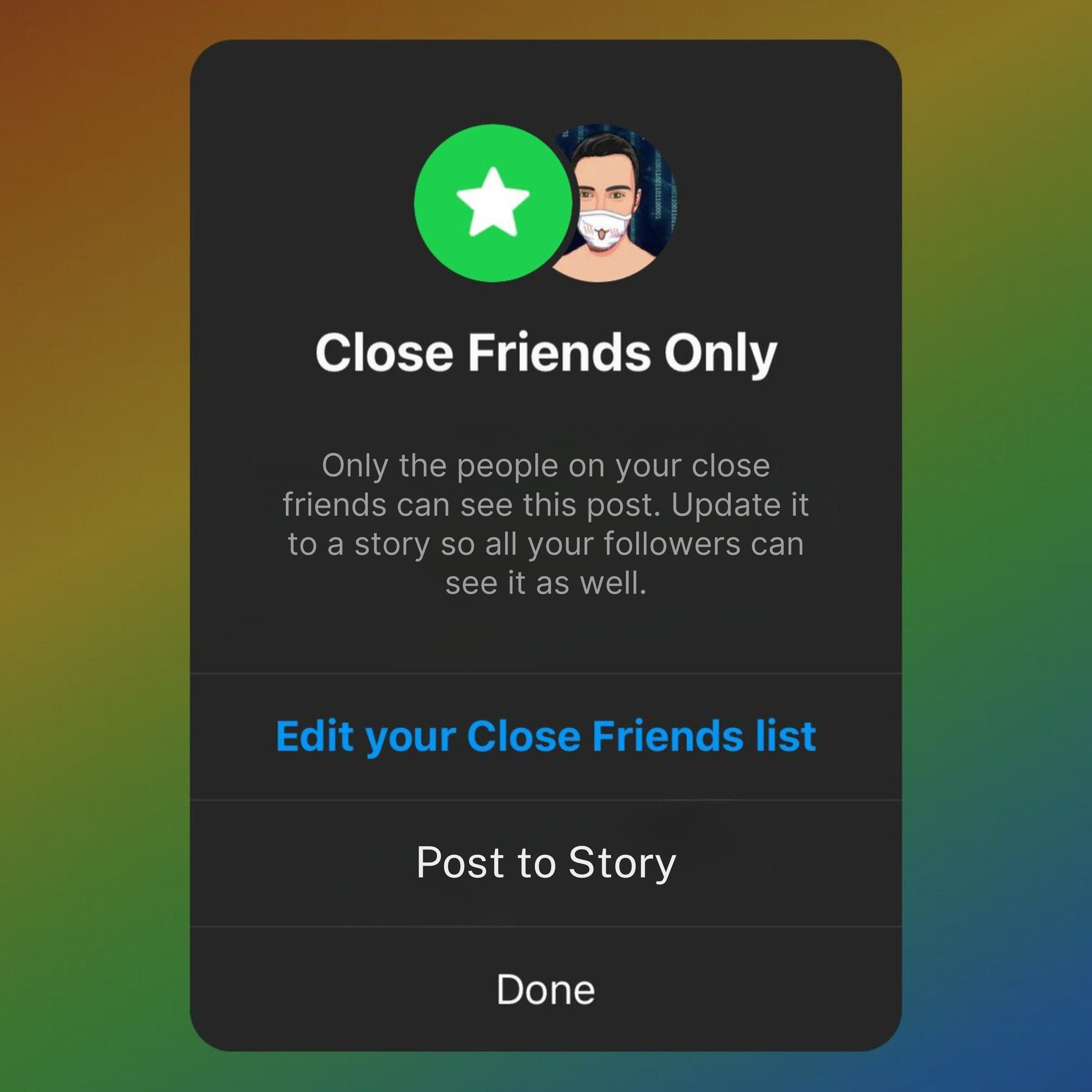
Includes tasks such as fraud prevention, literature reviews, content, websites and email marketing. A digital privacy and security concern igleak.info app has, of late, been in the news in the digital world According to its claims, it provides access. A large part of the stolen information is subsequently made public on internet databases, where it serves as the starting point for other illegal activities